According to arrest warrants obtained on Friday, a group of tech-savvy burglars who have been targeting homes in Connecticut and Massachusetts broke into a local residence. The burglars were able to gain access to the residence by obtaining detailed information on the security system from the homeowner’s co-worker.
Arrested on allegations of conspiracy to commit first-degree burglary and conspiracy to commit second-degree larceny is Matthew Colon, aged 31, residing in West Springfield, Massachusetts. Similarly, Enrique Santiago, a 37-year-old individual from Springfield, Massachusetts, is confronted with charges that include first-degree burglary, possession of burglary tools, theft of a firearm, and conspiracy.
The warrant for Colon reveals that the police are likely to detain a third man involved in the case. This investigation is intertwined with a series of other burglaries, which were executed using advanced surveillance techniques and insider knowledge about homeowners’ absence.
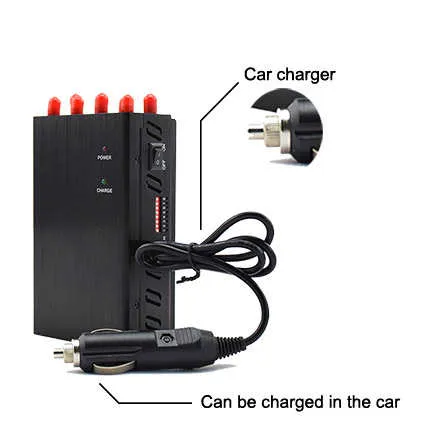
On May 20, 2022, a Long Island resident of Green Manor Terrace contacted the police, reporting that two men were seen walking through his backyard on a security camera. The officers who intervened in the burglary discovered a broken rear sliding glass door and a series of abandoned evidence near the property, such as a WiFi jammer, a two-way portable radio, a glass punch tool, a pry bar, and bolt cutters, as stated in the warrant.
As mentioned in the arrest warrant affidavit penned by Windsor Locks Detective Sgt. Jeff Lampson, the thieves were able to breach a chain link fence and disable surveillance cameras through both manual means and the use of a WiFi jammer. However, one camera located near the pool was not affected by the jammer device and remained operational, recording the incident. The homeowner reported the disappearance of US$4,200 in cash, along with men’s watches, jewelry, and his wife’s 9 mm pistol, according to the warrant.
The police have reported that on May 26, a pillowcase was uncovered by a resident living two houses away. Upon inspection, the pillowcase was found to contain watches, a handgun, and other items that were confirmed by the victims as their own. Following the break-in, the burglars fled in separate directions, as evidenced by the locations of the stolen bag of items and the backpack containing a wifi jammer.
According to Lampson’s statement on Friday, the use or operation of gsm jammer devices is not allowed by federal law and federal investigators are looking into the matter. Furthermore, he pointed out that the local police have witnessed a surge in the use of these devices in residential burglaries.
However, in this case, the police were able to conclusively prove the undoing of the thieves through DNA evidence. While conducting a thorough search of the Green Manor Terrace area during daylight hours on May 23, a homeowner came across a pair of gloves that she had not previously seen and immediately turned them over to the investigators. The police then submitted swabs taken from the gloves, along with other potential evidence believed to have been touched by the thieves, to the state forensic laboratory for analysis.
Lampson’s warrant stated that on August 16, the lab reported a DNA match on the gloves to Santiago, indicating the involvement of an offender. The police disclosed that the same DNA was linked to two prior burglary cases, one of which was a car break-in in Middletown from 2010, and the other was a burglary in South Hadley, Massachusetts in 2012, where firearms were stolen. Santiago was arrested in both instances, according to the warrant.
According to the warrant, Santiago relayed to the investigators from Windsor Locks, through his attorney, that the burglary at Green Manor Terrace was coordinated by a man driving a black sedan, whose father happened to own a remodeling company. Lampson, in the same warrant, documented that when he asked the homeowner if he was acquainted with an individual fitting that description, the homeowner promptly identified Colon, who worked alongside him at a home health care business in East Longmeadow, Mass.
According to the warrant, the homeowner expressed that he regarded Colon as a friend and had disclosed information about his visit to Long Island in May. The victim also mentioned that Colon and his father had aided him in remodeling his house. The warrant indicated that the homeowner stated that Matthew Colon had frequented his residence on numerous occasions and was fully aware of the surveillance camera system.
After being confronted with the victim’s statements and the evidence pertaining to the burglary, Colon admitted to the police that he had been manipulated into becoming involved in the scheme by the third suspect. The warrant indicates that the authorities anticipate the imminent arrest of the third suspect.
The suspect’s girlfriend was employed at the same home health care business as Colon and the victim from Windsor Locks. Lampson’s warrant stated that other employees of the company had their homes in Massachusetts burglarized. One woman claimed that Colon had been at her residence to fix a gazebo before the break-in.
The warrant stated that cellphone records provided evidence of phone calls between Colon, Santiago, and the unidentified suspect both prior to and following the Windsor Locks burglary. The police have described the third suspect as a convicted felon with a significant criminal background, which includes armed robbery and a series of burglaries.
Santiago’s extensive criminal record, as mentioned in the warrant, includes convictions for burglary and larceny in Connecticut. The Massachusetts investigators suspect his involvement in a criminal organization that specializes in targeted burglaries. Santiago has posted a bond of US$150,000 and is expected to make an appearance in the state Superior Court in Hartford on May 31. Similarly, Colon has posted a bond of US$100,000 and is scheduled to appear in court on May 2.